TL;DR
Retailers no longer fail because of weak firewalls — they fail because of weak SaaS governance. Customer data now flows across POS, e-commerce, loyalty, CDP, CRM, ERP, and marketing tools. Every integration is a potential exposure point, and one misconfigured API or stale IAM role can take critical systems offline or trigger million-dollar fines.
At the same time, regulations have hardened (GDPR, CCPA, PDPA, DPDP, PCI DSS 4.0). Third-party risk has surged with increasing API-level attacks and on top of that, business teams keep adopting new SaaS tools faster than IT can secure them.
Modern retail environments now require layered controls : IAM as the control plane, CASB and DLP to govern data movement, SIEM for detection and response, compliance automation for audit readiness, and Backup/DR for resilience. Security is no longer an IT project; it’s an operating posture that determines uptime, customer trust, and the speed at which you can scale.
Why Security & Compliance Can’t Be an Afterthought
A few years ago, most retailers treated security as an IT formality — something handled quietly in the background while teams focused on growth. Then breaches escalated, fines mounted, and customer trust eroded. AI-driven attacks got smarter, and suddenly security wasn’t a technical task; it was a board-level concern.
So what changed?
Data is now everywhere. Customer information flows through multiple channels- POS, e-commerce, loyalty programs, CDPs, marketing tools, and support desks. Every touchpoint is a potential breach. Meanwhile, third-party risk has exploded. You're only as secure as your weakest vendor. One breach in your CDP or helpdesk exposes millions of records. Don't forget the regulations which have further tightened. GDPR alone can fine up to 4% of a company’s global annual revenue for serious violations.
Make no mistake. The stakes are very high.
Customer trust is fragile. According to one report, 87% of shoppers won’t transact with brands they consider insecure. Breaches now cause downtime, lost revenue, and reputational damage. And as retailers add more SaaS, proprietary controls and misconfigurations create hidden operational risks. Proprietary controls can create vendor lock-in and slow down future migrations.
Bottom Line: One misconfigured API or weak access policy can shut down operations or trigger million-dollar fines. Moreover, compliance failures don't just damage trust; they kill uptime.
This is the environment in which retailers now make security and compliance decisions.
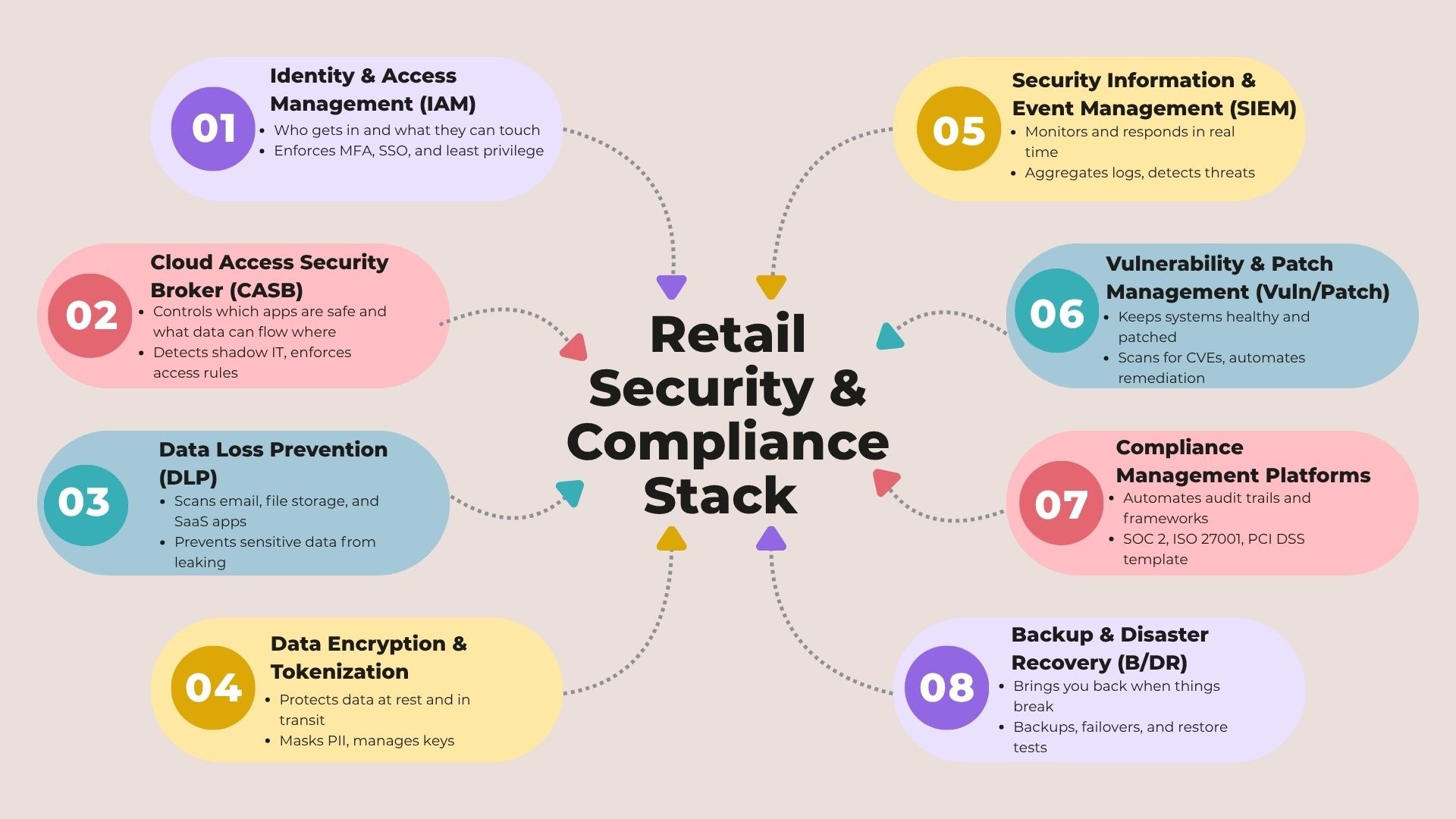
Core Security & Compliance Building Blocks
Security in retail SaaS isn't one purchase. It's a system that is layered, interconnected, and only as strong as its weakest link. Here's what actually matters for retailers and brands:
1. Identity & Access Management (IAM)
IAM is your front door. It decides who logs in, what they can access, and how much damage they can do if things go wrong. It centralizes authentication, enforces multi-factor authentication, and manages the entire employee lifecycle. It decides who gets access when they join, what changes when they switch roles, and what gets shut off when they leave.
Dependencies: Every SaaS app in your stack, clean SSO federation across all of them.
Watch-outs: Shadow accounts living outside your identity provider. Stale privileges sitting idle for months. Weak break-glass procedures when things go sideways.
Vendors: Okta, Auth0, Microsoft Entra ID, 1Password
2. Cloud Access Security Broker (CASB)
CASB identifies and governs the apps that your teams use including the shadow IT tools no one knows about. It enforces policies, monitors data movement, and applies inline controls to prevent unwanted access or risky usage.
Dependencies: Coverage of all cloud apps; traffic steering via agents or gateways.
Watch-outs: User friction if policies are too aggressive. Gaps in mobile or off-network traffic.
Vendors: Netskope, Zscaler, McAfee MVISION Cloud
3. Data Loss Prevention (DLP)
DLP watches what's moving through email, file shares, and SaaS apps. It flags or blocks anything that violates policy. It classifies customer PII and payment data before someone accidentally shares it in a Slack thread or a public Google Doc.
Dependencies: Email systems (M365, Gmail), file storage (Drive, SharePoint, Box), major SaaS apps.
Watch-outs: Over-blocking that kills productivity. Blind spots in third-party SaaS you forgot to connect.
Vendors: Nightfall, Varonis, Forcepoint
4. Data Encryption & Tokenization
Encryption locks down data at rest and in transit. Tokenization replaces sensitive fields—PII, payment data—with meaningless placeholders in apps and APIs.
Dependencies: Databases, data lakes, integration layers, payment flows.
Watch-outs: Orphaned keys or expired certificates. Performance hits if not designed properly.
Vendors: Protegrity, Thales CipherTrust, AWS KMS
5. Security Information & Event Management (SIEM)
Think of SIEM as mission control. It aggregates logs from across your environment, looks for patterns, and triggers alerts or automated responses when something looks off.
Dependencies: Logs from your identity provider, POS and e-commerce systems, endpoints, cloud infrastructure, critical SaaS apps.
Watch-outs: Alert fatigue from too many false positives. Ingesting noisy logs without filters is expensive and distracting.
Vendors: Splunk, Sumo Logic, Datadog Security
6. Vulnerability & Patch Management
This scans for known vulnerabilities and misconfigurations. It prioritizes what actually matters and automates fixes where possible.
Dependencies: Endpoint management, CI/CD pipelines, cloud inventory.
Watch-outs: "Found but unfixed" backlogs piling up. Blind assets like BYOD devices, lab environments, or new cloud accounts that no one is tracking.
Vendors: Qualys, Rapid7, Tenable
7. Compliance Management Platforms
These platforms map your controls to frameworks like GDPR, PCI DSS, and SOC 2. They automate evidence collection and spit out audit-ready reports.
Dependencies: Integrations with your identity provider, cloud platforms, ticketing systems, code repos, HRIS, and key SaaS apps.
Watch-outs: "Automated" controls that still need human review: DPIAs, PCI scope, DPDP nuances.
Vendors: Vanta, Drata, Secureframe, Sprinto
8. Backup & Disaster Recovery (B/DR)
Policy-based backups. Immutable copies. Fast restore and failover. When systems go down, this is what keeps the lights on.
Dependencies: All critical systems and data stores. Clear recovery point objectives (RPO) and recovery time objectives (RTO) for each system—POS, OMS, payroll.
Watch-outs: Untested runbooks. Backup jobs showing green, but restores failing when you need them. Single-region risk.
Vendors: Veeam, Druva, Rubrik, Cohesity
The Trade-Offs: What You'll Have to Balance
Security isn't a checklist. It's a set of choices, each with consequences. Understanding these tensions is what separates resilient stacks from brittle ones. Here's where most
- Bundled vs. Best-of-Breed
You can go with a cloud suite like Microsoft 365 Security or AWS Security Hub and get simplicity. Or you can stack specialized tools like Okta, Netskope, and Vanta for deeper functionality.
Reality : Most teams start bundled. As audit requirements expand and complexity grows, they start adding best-of-breed pieces.
Watch out: Integration overhead. Every new tool means connectors, SSO mapping, and policies that need to work together. Budget for it upfront.
- Automated vs. Manual Compliance
Platforms like Vanta, Drata, and Sprinto promise speed and scale. They'll collect evidence automatically and generate reports. But frameworks like GDPR, PCI DSS, and India's DPDP Act still need human interpretation.
Reality: You'll hit around 70% automation. The other 30% that entails policies, data protection impact assessments, and legal nuance still requires human judgment.
Watch out: "SOC 2-ready" doesn't mean auditor-ready. Ask how controls map to each framework. Ask if you can export clean evidence packs. If the answer's vague, keep digging.
- Preventive vs. Detective Controls
Preventive controls lock things down upfront: IAM, multi-factor authentication, patching. Detective controls find problems after they happen: SIEM, CASB, DLP.
Reality: You need both. Prevention shrinks your attack surface. Detection limits the damage when something slips through.
Watch out: Lean too hard on prevention and users get frustrated. Lean too hard on detection and you drown in alerts.
- Global Standards vs. Local Laws
Frameworks like SOC 2, ISO 27001, and PCI DSS are universal. Regional laws such as GDPR, CCPA, PDPA, and India’s DPDP Act impose additional requirements on data residency, consent, and retention.
Reality: Passing SOC 2 doesn’t make you compliant across Asia or Europe. Data residency, consent workflows, and retention rules still need separate attention.
Watch out: Always verify where data (and encryption keys) actually live. Check retention policies for each market you operate in.
- Cost of Ownership vs. Cost of Breach
Security costs money in licenses, integrations, and talent. Breaches cost more in response, downtime, fines, and lost trust. Prevention is almost always cheaper than cleanup.
Reality: IBM’s 2024 numbers show mid-market breaches approaching $3M on average.
Watch out: Don't forget the hidden costs: SIEM tuning, chasing false positives, on-call burnout, redoing work after failed audits.
- Vendor Consolidation vs. Redundancy
Fewer vendors simplify operations but create single points of failure. More vendors reduce concentration risk but increase coordination overhead.
Reality: If your IAM goes down, stores must still be able to access POS, payroll, and support tools.
Watch-out: Always build at least one break-glass path (secondary IdP, cached roles, offline modes).
- Automation vs. Expertise
Tools enforce rules; people govern them. Automation only works when someone owns IAM policies, DLP rules, and access reviews.
Reality: Security platforms reduce effort, not accountability.
Watch-out: Quarterly evidence checks and policy updates are non-negotiable.
- Visibility vs. Velocity
Stricter controls slow down SaaS onboarding. Looser controls increase adoption but expand the attack surface.
Reality: Tiered onboarding solves both: fast-track low-risk tools and run deeper reviews for anything touching PII or payments.
Watch-out: Seasonal exceptions (Black Friday, quarter-end) must expire automatically.

Evaluation Framework: How to Compare Security & Compliance Tools
Knowing the trade-offs is one thing. Comparing vendors across different categories, pricing models, and levels of maturity, is however another. This framework helps you score each solution on the criteria that actually determine retail fit.
Score each vendor from 1 (basic) to 5 (advanced) across the dimensions below.
1. Integration Breadth
What to assess: Native connectors across your SaaS stack (POS, e-commerce, CRM, HRIS, CDP, cloud), API/webhook fallbacks, and two-way sync capabilities.
How to assess: Map your full stack, request the vendor’s connector catalog, validate data flows in a pilot.
2. Regulatory Coverage
What to assess: Support for GDPR, CCPA, PDPA, DPDP, PCI DSS, SOC 2, ISO 27001 plus data residency options.
How to assess: Review control-to-framework mapping documentation and verify exportable, auditor-acceptable evidence.
3. Time to Compliance
What to assess: Median onboarding-to-audit timelines, % of controls automated, and readiness playbooks.
How to assess: Ask for SOC 2 timelines for similar customers; validate automated evidence collection in a sandbox.
4. Alert Quality & Noise
What to assess: Signal-to-noise ratio, alert correlation, and tunability (thresholds, suppression, routing).
How to assess: Review sample alert logs and test tuning during a controlled pilot.
5. Incident Response Speed
What to assess: Detection-to-containment time, playbook depth, automated remediation, and integrations with ticketing/pager tools.
How to assess: Simulate an incident end-to-end; evaluate one-click containment and post-incident reporting.
6. Scalability & Performance
What to assess: Data/tenant limits, API throughput, latency SLAs, and peak-load performance.
How to assess: Request load-testing results; validate performance under projected 3-year growth.
7. Data Residency & Encryption
What to assess: Regional hosting options, encryption at rest/in transit, key management, tokenization support.
How to assess: Confirm where data and encryption keys physically reside.
8. Vendor Security Posture
What to assess: SOC 2 Type II or ISO 27001 certification, pen-test cadence, vulnerability disclosure policies, breach history.
How to assess: Review certificates, pen-test summaries, and incident disclosures under NDA.
9. Total Cost of Ownership (3 Years)
What to assess: Licensing, integrations, admin FTE, SIEM ingestion costs, audit cycles, training, and breach insurance impact.
How to assess: Model user/data growth and recertification cadence before committing.
Buyer Checklist (Answer Before Shortlisting)
- What customer data do we collect, where does it live, and which systems process it?
- Which regulations apply today — and which will apply as we enter new regions?
- What’s our current breach risk profile (pen-test results, known gaps, shadow IT)?
- Can the tool integrate with our existing stack without custom middleware?
- How long will it take to get SOC 2 or PCI DSS audit-ready with this vendor?
- Do we have the in-house expertise to operate this tool?
- How does the vendor handle data residency, encryption, and key management?
- What is their incident response SLA, and what happens if they get breached?
- Can we export all logs and audit trails, or are we locked into proprietary reporting?
- What is our exit plan if pricing changes or acquisition risk increases?
Final Guidance or Scenario Fit
You've scored the vendors and answered the hard questions. Now map the right architecture to your reality, anchored to your revenue, complexity, and how fast you're moving.
1) Digital-Native & Fast-Growing Brands
(D2C / CPG | Lean teams | <$10M today | scaling cross-border)
Recommended Approach: Integrated Core + Minimal Add-Ons
Small, digital-native brands rarely build big security stacks. They lean on an integrated core: Shopify plus Google Workspace or Microsoft 365. Lower cost. Fewer dashboards. Native coverage is “good enough” until bigger contracts arrive. A few focused add-ons handle most of the compliance lift.
Recommended Stack
- Integrated core (your “suite”):
- Platform Security: Shopify’s native protections (payments, store access, app permissions)
- Workspace / M365 Security: MFA, device management, spam/phishing filters
- Minimal add-ons (to close critical gaps)
- IAM (App/Auth): Auth0 for consumer login (including social login
- Compliance Automation: Vanta, Drata, or Secureframe to get SOC 2 and privacy controls audit-ready
- Password Management: 1Password or Dashlane for employee credentials
- Only when you start scaling harder
- Optional: Datadog Security Monitoring (basic SIEM) and Nightfall (DLP) once you see real traffic, sensitive data flows, or investor pressure.
Watch-Out: Enable consent flows early for EU and California. Keep employee SSO (Workspace) separate from consumer SSO (Auth0) to avoid privilege creep.
2) Scaling Omnichannel Retailers
(10–200 stores | POS + e-commerce + ERP + CDP)
Recommended Approach:
A hybrid security stack - integrated suites for foundational controls, with best-of-breed tools added where omnichannel risk is highest.
Retailers at this stage run physical stores and e-commerce simultaneously. Data flows across POS, OMS, WMS, ERP, CRM, and CDP systems. Payment processing makes PCI DSS mandatory, and multi-role access models span store managers, cashiers, warehouse teams, and HQ. An integrated suite alone isn’t enough, but a full enterprise GRC stack is overkill. The right fit is a hybrid.
Recommended Stack
- IAM: Okta or Microsoft Entra ID
- CASB: Netskope or Zscaler
- SIEM: Splunk or Sumo Logic
- DLP: Nightfall or Varonis
- Compliance Automation: Vanta or Drata
- Backup & DR: Veeam or Druva
Optional Add-Ons:
- Secrets management (1Password Business)
- API security scanners (Salt / Noname) for custom integrations
Watch-Out: Budget realistically for PCI DSS, because quarterly scans and annual audits add up. Avoid SIEM over-ingestion. It leads to noise and runaway costs.
3) Enterprise-Lite Retail Chains
(200+ stores | multi-region operations | hybrid cloud + legacy ERP)
Recommended Approach:
A specialized, enterprise-grade security stack — built for governance, auditability, advanced encryption, and region-aware controls across GDPR, CCPA, DPDP, and PCI DSS.
Retailers at this scale operate across multiple markets, with hybrid infrastructure, layered approval workflows, and large identity volumes. Legacy ERP and on-prem systems increase integration complexity. This is where security shifts toward best-of-breed enterprise tooling.
Recommended Stack
- IAM: Microsoft Entra ID + on-prem Active Directory integration
- SIEM: Splunk Enterprise Security
- CASB: McAfee MVISION or Netskope
- GRC / Compliance: ServiceNow GRC or RSA Archer (Vanta/Drata/Secureframe/Sprinto still useful for SOC/ISO automation)
- Encryption & Tokenization: Thales CipherTrust or AWS KMS
- Backup & DR: Rubrik or Cohesity
Optional Add-Ons:
- Privileged Access Management (CyberArk)
- Data lineage and cataloging (Collibra, BigID)
Watch-Out: Enterprise tools create vendor lock-in. Negotiate data portability clauses upfront. Ensure tokenization and key management policies don't break legacy ERP workflows.
The fact is that your stage defines your stack. But the underlying principle doesn't change:
Security isn't something you add later. The right stack lets you move fast without breaking trust. The wrong stack turns into a compliance nightmare, slows down launches, and opens you up to fines and breaches.
Golden rules:
- Start with foundational hygiene: MFA, password management, SOC 2.
- Layer in specialized tools as complexity grows: SIEM, CASB, DLP.
- Own your audit trail: Don't rely on vendor-locked reporting.
- Vet your vendors harder than they vet you: Your security is only as strong as your weakest SaaS tool.
Security and compliance aren't IT problems. They're business enablers. Build it into your stack from Day 1.
Next Steps
- Audit your current exposure. Map where customer data lives. Identify unmonitored SaaS tools.
- Pick your first certification. SOC 2 is the baseline for B2B deals. PCI DSS is non-negotiable for payments.
- Pressure-test your vendors. Use the checklist above. If they can't answer, that's your answer.
Start secure. Scale confidently.
.png)

.avif)


.avif)